Tag Archives: routing
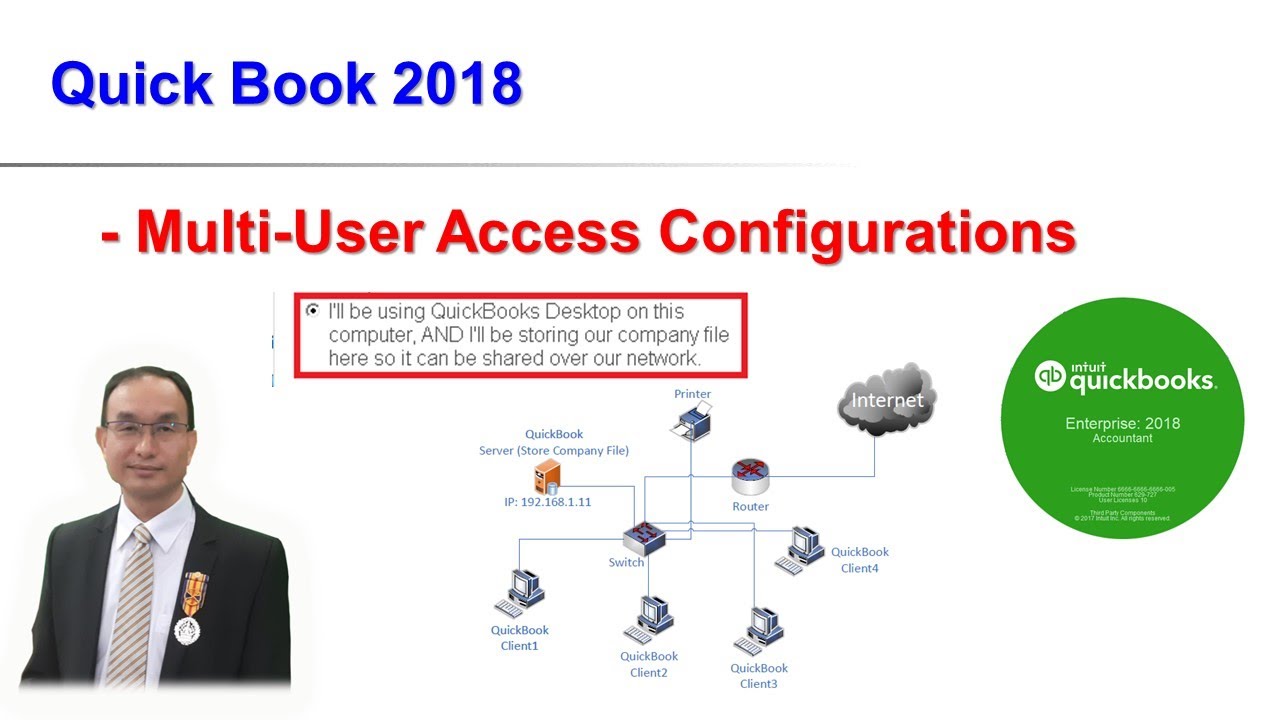
How to configure Quick Book for Supporting Multi-User Access
accessbuntha chhaycambodia comptuer networkcambodia lectureCambodia universitychapter1computer network teaching in khmerComputer NetworksConfiguredata communicationshosting mumti-user accesshowintroductionintroductions to data communicationskhmer itkhmer it lessonkhmer lecturekhmer lessonkhmer teachingLabmulti-user accessnetworkquickbookquickbook serverrouterroutingspeak khmersub-interfaceswitchteaching in khmervlan

Install and Configure Web Server and DNS Server on Windows server 2012 R2
buntha chhaycambodia comptuer networkcambodia lectureCambodia universitycomputer network teaching in khmerComputer NetworksConfiguredata communicationsdns serverhowintroductionintroductions to data communicationskhmer itkhmer it lessonkhmer lecturekhmer lessonkhmer teachingLabnetworkPractic Exercise on DNS and Webrouterroutingspeak khmersub-interfaceswitchteaching in khmertracertrunkvlanWeweb serverwindows server 2012 r2

WHAT IS A CIDR IN AWS? | VPC PART 2 | Visual Explanations
Amazon Web ServicesAWSaws subnetting tutorialCIDRcidr blockcidr block in awscidr calculationscidr notationcidr notation explainedcidr subnet bitscidr subnetting tutorialclassless inter-domain routingclassless ip addressing exampleIP AddressnetworkingPythoholicpythoholic awsRoadToAWSroutingsaa-c02subnetsubnet cidr chartsubnet masksubnettingsubnetting tutorialVirtual Private Cloudvirtual private cloud awsvpc cidr blockwhat is cidr
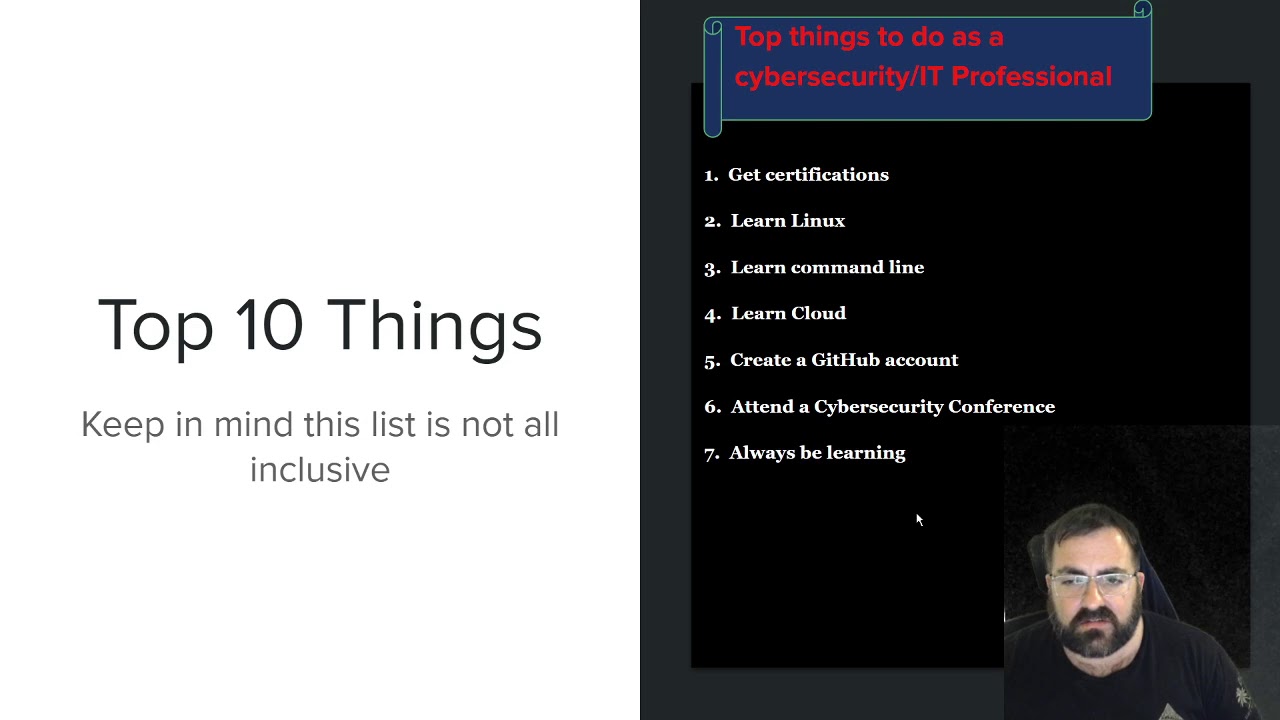
Ethical Hacking Episode 2: Top 10 things Cybersecurity #Cybersecurity #security #infosec #ceh
blueteamcehcomptiaComputer sciencecomputingcyber securitycyber security trainingCybersecurityCyberSecurity 101cybersecurity 2021cybersecurity careerscybersecurity for beginnersEC-councileccouncilethical hackingethical hacking 101ethicalhackingethicalhacking for beginnersfirewallsInfosecIoTitIT skillslet's talk cyber securitynetworkingnew to cybersecurityRaspberry piredteamroutingSecuritysmartphonesswitchingtechwireless



Create OU User and Group Map Drive in Domain Controller in Windows Server 2012 R2
accessbuntha chhaycambodia comptuer networkcambodia lectureCambodia universitychapter1computer network teaching in khmerComputer NetworksConfigurecreate OUdata communicationsFile Server on Windows server 2012R2Groupshowintroductionintroductions to data communicationskhmer itkhmer it lessonkhmer lecturekhmer lessonkhmer teachingLabnetworkpacketpermissionroutingspeak khmersub-interfaceteaching in khmertracertrunkUsersvlan

Using Pod Security Policies to harden your Kubernetes cluster
2019alertingArchitectureautomatebountybugcertificatecloudclusterdefenseDevopsDevSecOpsDistributedElixirencryptionengineeringfeedbackfunctionalhasgeekKafkakeykuberneteslogmaliciousmanagementmanagermonitoringmultinetworkOLAPOLTPOnionOpenopenscapOSINTpodpolarDBPolicyprogrammingpythonreliabilityremoterootconfroutingSecurityServersourceSRESSHstreamsSystemtenantTortrafficusabilityUserVitessWireshark

Scale MySQL beyond limits with ProxySQL
2019alertingArchitectureautomatebountybugcertificateclouddefenseDevopsDevSecOpsDistributedElixirencryptionengineeringfeedbackfunctionalhasgeekKafkakeylogmanagementmanagermonitoringOLAPOLTPOnionOpenopenscapOSINTpolarDBprogrammingpythonreliabilityremoterootconfroutingSecurityServersourceSRESSHstreamsSystemTorVitessWireshark
Recent Posts
- Java Collection in Tamil What is Collection – Collection in Tamil – Java in Tamil – Payilagam
- Lesson 5 – Keeping Score
- What is Jakarta EE? and why it does matter for Java enterprise?
- Java in Tamil – Arrays Introduction for Beginners – Muthuramalingam – Payilagam
- Data Security: Improving Your Cyberhygiene
