Tag Archives: malware detection
Day 1 Part 6: Rootkits: What they are, and how to find them
bootkitsclassescomputer securitycomputer security classcyber securityDKOMeducationhookingHost SecurityIAT hookingIDT hookinginline hooksIRP hookingKOHmalwaremalware detectionmulti-day-classmulti-day-trainingOpenSecurityTraining.inforootkit detectionRootkitsSSDT hookingstealth malwaretrainingWindows rootkitsx86 assembly
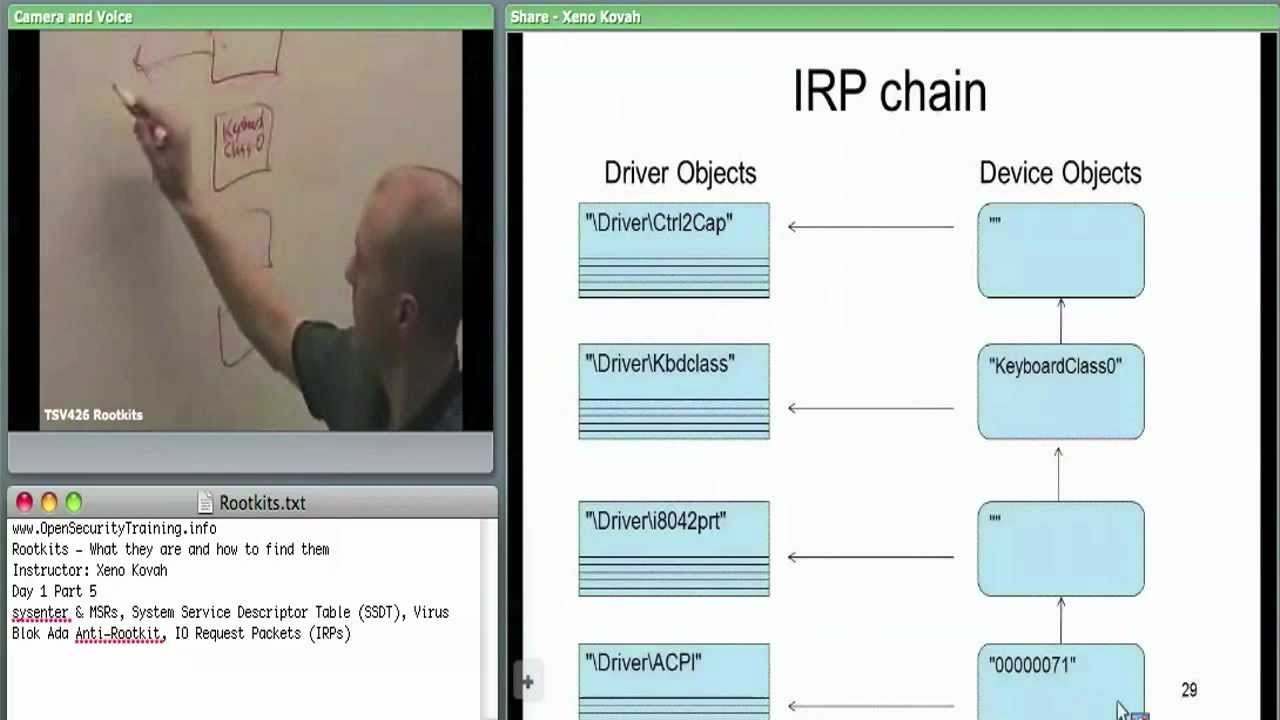
Day 1 Part 5: Rootkits: What they are, and how to find them
bootkitsclassescomputer securitycomputer security classcyber securityDKOMeducationhookingHost SecurityIAT hookingIDT hookinginline hooksIRP hookingKOHmalwaremalware detectionmulti-day-classmulti-day-trainingOpenSecurityTraining.inforootkit detectionRootkitsSSDT hookingstealth malwaretrainingWindows rootkitsx86 assembly
Recent Posts
- What’s New in Parallels RAS 18.1
- DevOps & SysAdmins: Trying to use Azure AD as LDAP server with Cisco Catalyst IP Base
- Understanding Microsoft Azure AD SSO with non-persistent VDI (Instant Clones)
- How to host AspNet MVC app for free in #Azure #AppServices || Bangla Tutorial
- Raspberry Pi: Connect Raspberry Pi to Azure IoT Hub
