Tag Archives: computer security class
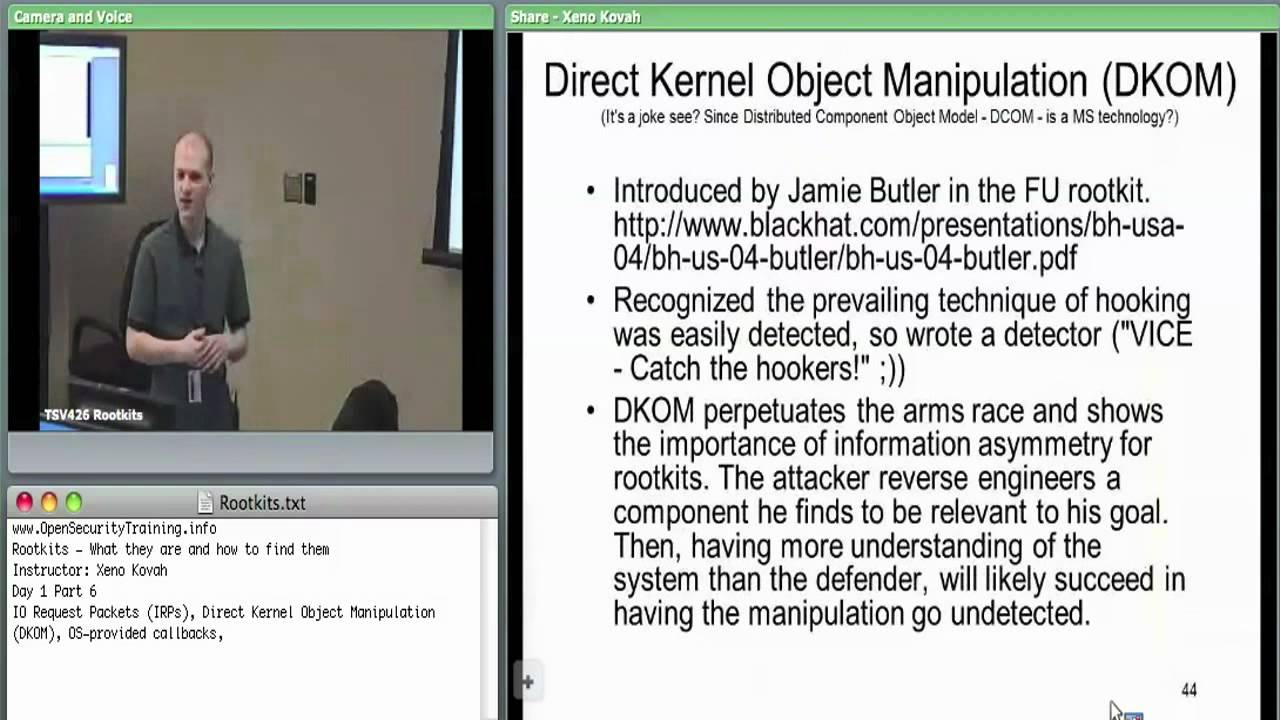
Day 1 Part 6: Rootkits: What they are, and how to find them
bootkitsclassescomputer securitycomputer security classcyber securityDKOMeducationhookingHost SecurityIAT hookingIDT hookinginline hooksIRP hookingKOHmalwaremalware detectionmulti-day-classmulti-day-trainingOpenSecurityTraining.inforootkit detectionRootkitsSSDT hookingstealth malwaretrainingWindows rootkitsx86 assembly
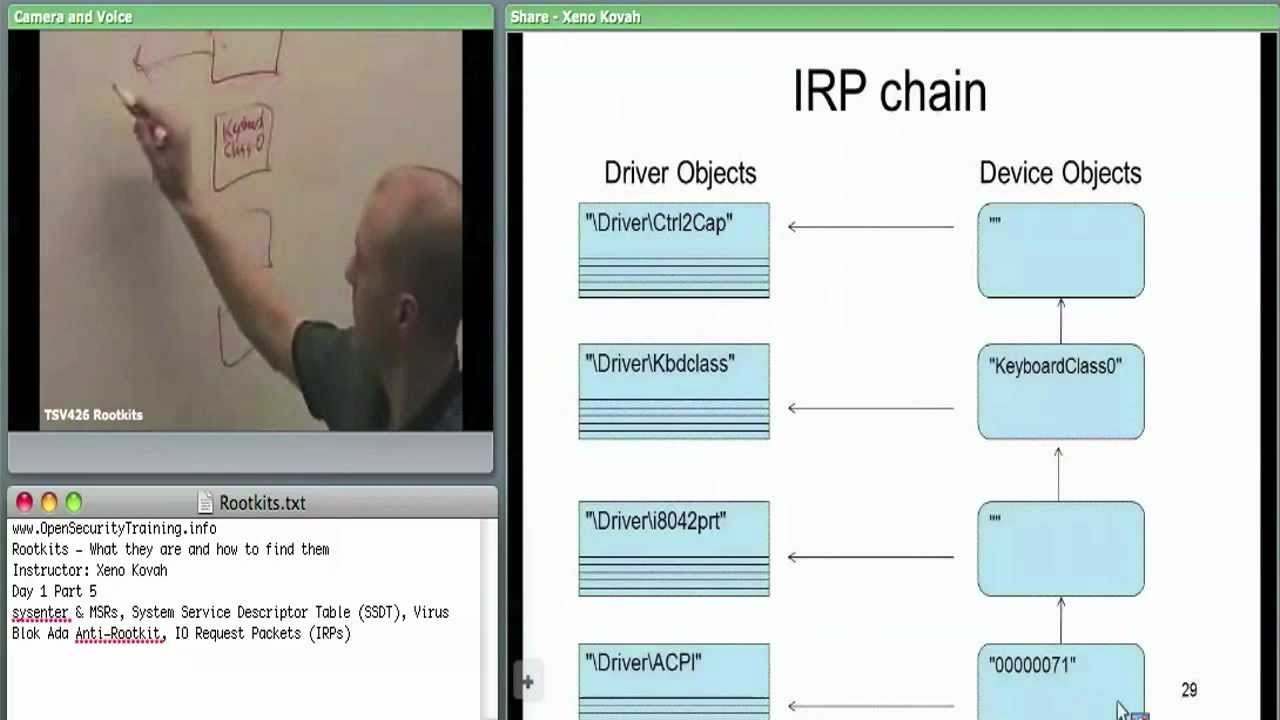
Day 1 Part 5: Rootkits: What they are, and how to find them
bootkitsclassescomputer securitycomputer security classcyber securityDKOMeducationhookingHost SecurityIAT hookingIDT hookinginline hooksIRP hookingKOHmalwaremalware detectionmulti-day-classmulti-day-trainingOpenSecurityTraining.inforootkit detectionRootkitsSSDT hookingstealth malwaretrainingWindows rootkitsx86 assembly

Day 1 Part 2: Intro Trusted Computing
attestationAuthenticationclassesComputercomputer securitycomputer security classcryptographycyber securityCybersecuritydecryptiondigital signaturesDRTMdynamic root of trusteducationencryptionOpenSecurityTraining.infoPCRPCRsSecuritySRTMstatic root of trustTPMtrainingtrustTrusted ComputingTrusted Computing Grouptrusted hardwareTrusted Platform Module
Recent Posts
- Access Control, update 2015 – George Danezis
- CSIAC Webinar: Users Are Not Stupid: Eight Cybersecurity Pitfalls Overturned
- “PM Modi is very wise man” Putin calls for cooperation with India in financial security, cybercrime
- Bandwidth.com And The Ongoing DDoS Attacks Against VoIP Providers
- Java Collection in Tamil What is Collection – Collection in Tamil – Java in Tamil – Payilagam
