Tag Archives: key

Automate your IX’s RS Config
2019alertingArchitectureautomatebountybugcertificateclouddefenseDevopsDevSecOpsDistributedElixirencryptionengineeringfeedbackfunctionalhasgeekKafkakeylogmanagementmanagermonitoringOLAPOLTPOnionOpenopenscapOSINTpolarDBprogrammingpythonreliabilityremoterootconfroutingSecurityServersourceSRESSHstreamsSystemTorVitessWireshark

EYE on NPI – Authentrend FIDO Biometric Security Keys #EyeOnNPI @DigiKey @adafruit @authentrend
ada fruitadafritadafruitadafruit couponsadafruit promo codeAIarduinoAuthentrendbiometriccircuitplaygoundcircuitpythonComputerDigi-KeyDigiKeydiyelectronicsEYE on NPIFIDOFIDO2hardwarekeyladyadalimorlimorfriedloginmachine learningmakemakersmicrobitMicrocontrollersmicropythonneopixelneopixelsnewNew ProductNPInycopensourcepiprojectspythonraspberryRaspberry piraspberry pi zeroraspberrypisecureSecuritysteamSTEMtensorflowUsb

How iPhone thieves are locking owners out of devices l GMA
abcabc newsapple newsgmagood morning americahackersiphoneiphone hacked how to telliphone hacked what to doiphone hackingiphone hacks 2023iphone newsiphone recovery keyiphone recovery key hackiphone recovery key thievesiphone scamsiphone wall street journaliphone wsjjournalkeynewsp_cmsid=2494279p_vid=news-98718438recovery”Securitystreettech newswallwsj.
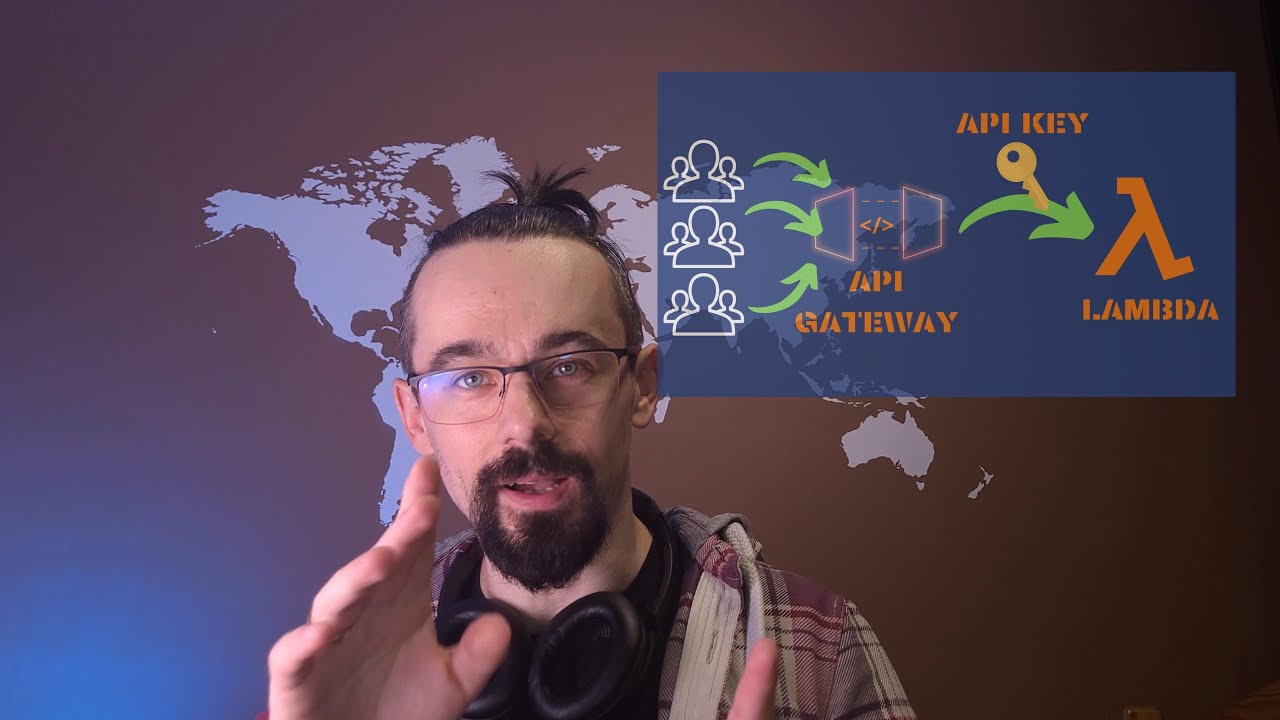
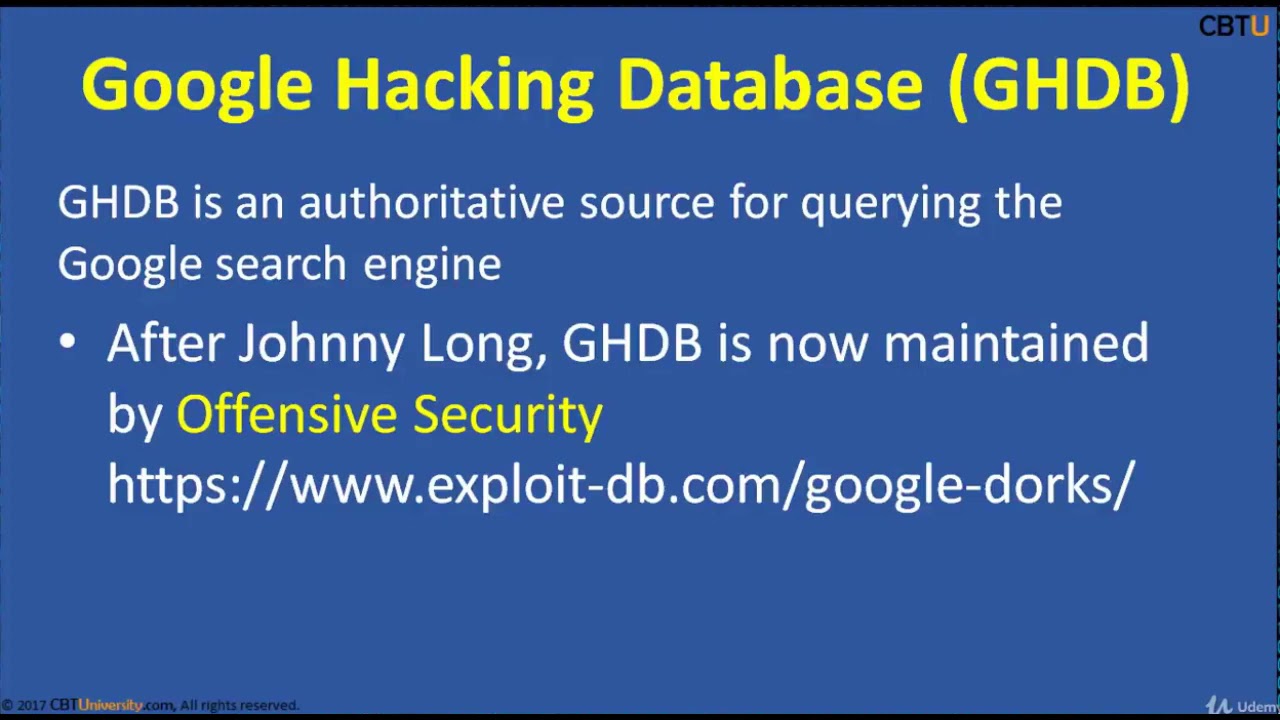
CEH2-3 Google Hacking Dorking
2015additionsaircrackbasicsBeginnersblackclicommandCompletecoursecrackcrackingenvironmentethicalexpertfootprintingforfreegreyguesthackhackerHacker (Interest)hackershackingHackshathdinstallinterfaceitKalikeylearn hacking in banglalineLinuxliveloggersmacchangernetworknmaponlinepenetrationprivateproxychainsreaverSecurityskillsSQLtermstestingtrainingUdemyvirtualvirtualboxVirtualBox (Software)vpnvpswhitewifiWindowswpawpa2
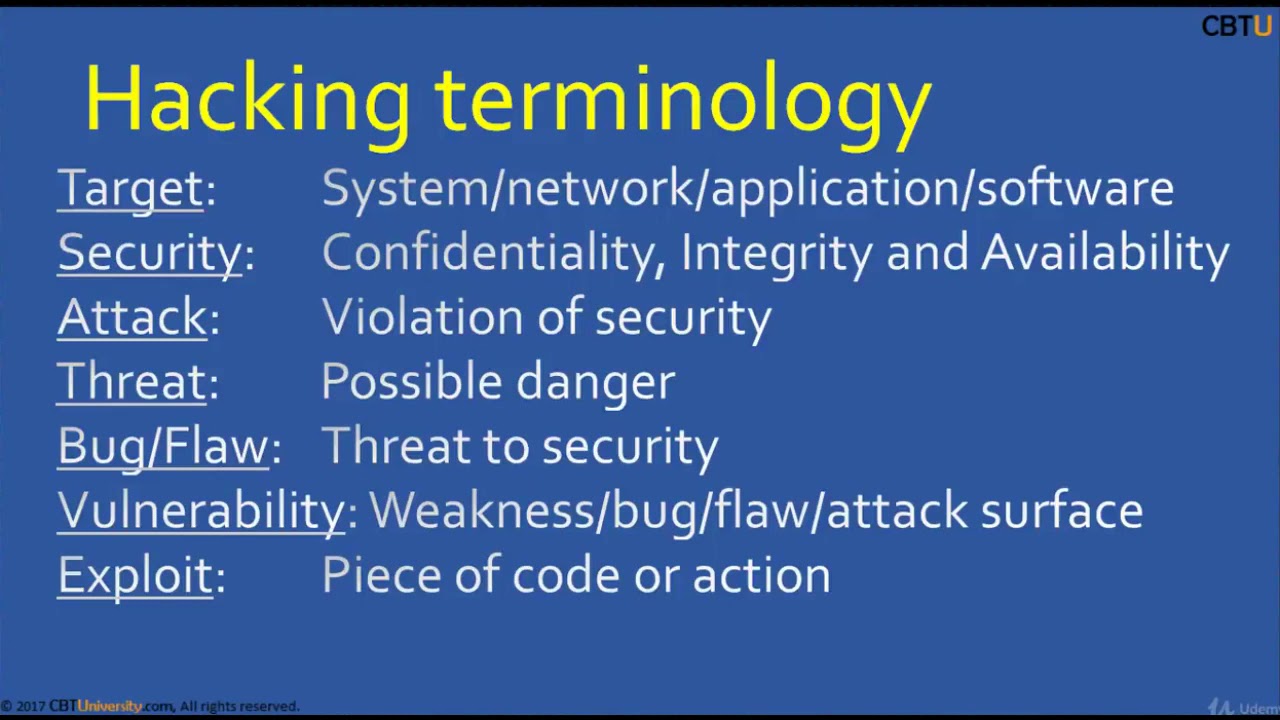
CEH1-1 Introduction to hacking
2015additionsaircrackbasicsBeginnersblackclicommandCompletecoursecrackcrackingenvironmentethicalexpertfootprintingforfreegreyguesthackhackerHacker (Interest)hackershackingHackshathdinstallinterfaceitKalikeylearn hacking in banglalineLinuxliveloggersmacchangernetworknmaponlinepenetrationprivateproxychainsreaverSecurityskillsSQLtermstestingtrainingUdemyvirtualvirtualboxVirtualBox (Software)vpnvpswhitewifiWindowswpawpa2


Using Pod Security Policies to harden your Kubernetes cluster
2019alertingArchitectureautomatebountybugcertificatecloudclusterdefenseDevopsDevSecOpsDistributedElixirencryptionengineeringfeedbackfunctionalhasgeekKafkakeykuberneteslogmaliciousmanagementmanagermonitoringmultinetworkOLAPOLTPOnionOpenopenscapOSINTpodpolarDBPolicyprogrammingpythonreliabilityremoterootconfroutingSecurityServersourceSRESSHstreamsSystemtenantTortrafficusabilityUserVitessWireshark

Scale MySQL beyond limits with ProxySQL
2019alertingArchitectureautomatebountybugcertificateclouddefenseDevopsDevSecOpsDistributedElixirencryptionengineeringfeedbackfunctionalhasgeekKafkakeylogmanagementmanagermonitoringOLAPOLTPOnionOpenopenscapOSINTpolarDBprogrammingpythonreliabilityremoterootconfroutingSecurityServersourceSRESSHstreamsSystemTorVitessWireshark
Recent Posts
- replacefirst And Replaceall Method Of String Class In Java |Part138| Core Java By Java Professional
- Java tutorial for beginners – User Input, Expressions (Part 4) | XPERGE
- Format Specifiers Example: Java 11 For Complete Beginners 027
- Addition: Java 11 For Complete Beginners 013
- M365 Transformations: Awareness Training
