Tag Archives: cyber attack




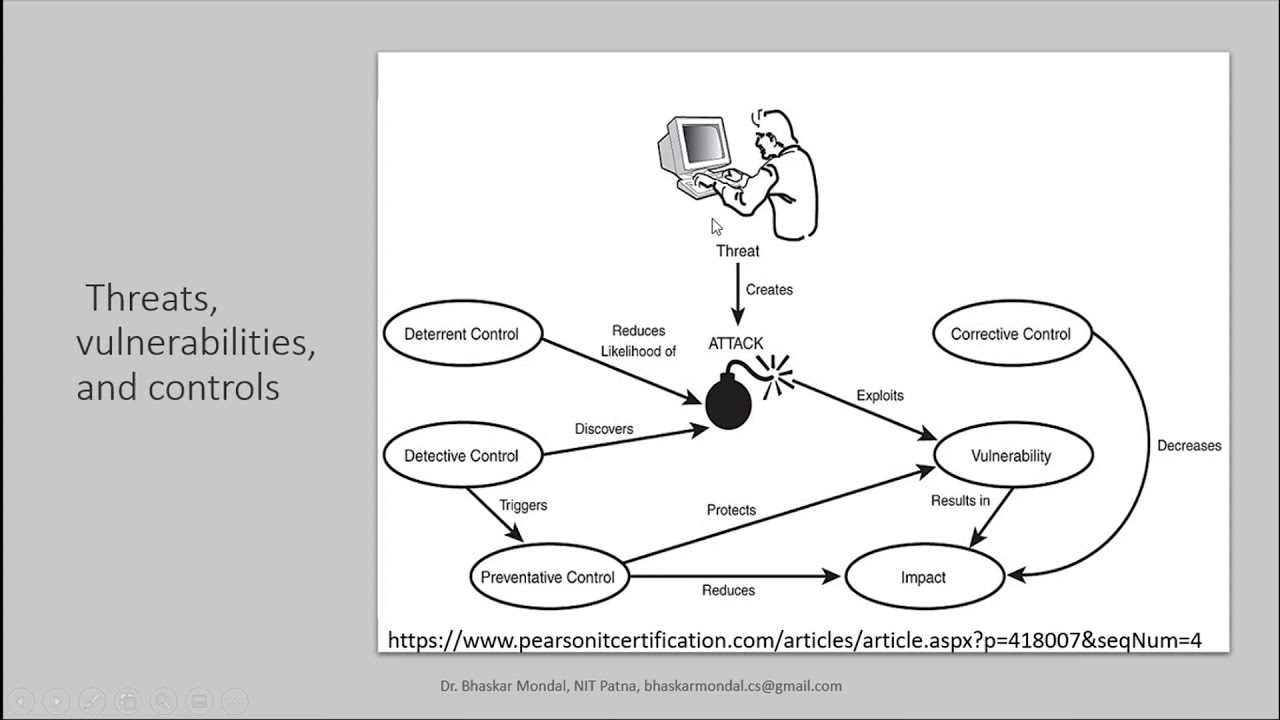
Threats, vulnerabilities, and controls in Information Security
Access ControlAESAIassignmentcode for beginners tutorialcomputecrypto systemcryptographycyber attackcyber securityDBMSdecryptiondeep learningDESdiyECCencryptionFLATguideHow toIDSinformation securityinstallintrusion detectionLATEXlearn to programlecturemachine learningMLNetwork Securityprivate keyprogrammingpublic keypythonrsascientific computingSecuritySHASQLTOCtutorial“computer laboratory” computer science GATE
Keynote Talk on Cyber Security and Symmetric Key Encryption
Access ControlAESAIassignmentcode for beginners tutorialcomputecrypto systemcryptographycyber attackcyber securityDBMSdecryptiondeep learningDESdiyECCencryptionFLATguideHow toIDSinformation securityinstallintrusion detectionLATEXlearn to programlecturemachine learningMLNetwork Securityprivate keyprogrammingpublic keypythonrsascientific computingSecuritySHASQLTOCtutorial“computer laboratory” computer science GATE

Secure Network Architecture for the Cloud
account hijackingAngus MacTechapisCloud SecurityCloud Security AllianceCSAcyber attackCyber crimecyber securitydata lossdata managementDiversificationEconomyEnergyGlobalizationGordon BruceHawaiiHibachi TalkPete InsallPeter InsallpopularPresidioPresidio West CoastPrivate CloudPublic CloudRick Trejosecure network architecturesecurity networkSoftware EngineeringtechThink Tech Hawaii


Cyber Security Awareness Video 2018 | Cyber attack | Thoughtful Show | S01E08
business internet securitycloud security servicescybercyber attackCyber crimecyber securitycyber security jobscyber security online degreecyber security salarycyber security teaminformation securityInternet securitynadirnadir alinet securityNetwork Securityp4 pakaop4 pakao 2018p4 pakao valentine day prankThoughtful showvalentine day prankvalentine's day prank
Recent Posts
- CSIAC Webinar: Users Are Not Stupid: Eight Cybersecurity Pitfalls Overturned
- “PM Modi is very wise man” Putin calls for cooperation with India in financial security, cybercrime
- Bandwidth.com And The Ongoing DDoS Attacks Against VoIP Providers
- Java Collection in Tamil What is Collection – Collection in Tamil – Java in Tamil – Payilagam
- Lesson 5 – Keeping Score
