Tag Archives: Zero to Hero

CEH18-3 Cloud Security Alliance
#Shells#TesteraircrackbasicsBeginnersburp suiteCompletecourseCybersecurityenumerationethicalethical hackerexpertfootprintingfreehackingHacking CourseHacking For Beginnershacking tutorialinformation securityInfosecitlearn hacking in banglamacchangermetasploitnmaponlinepass the hashpenetrationpenetration testerPentesterport scanningproxychainsreport writingreverse shellSecuritySQLtestingtrainingUdemyZero to Hero
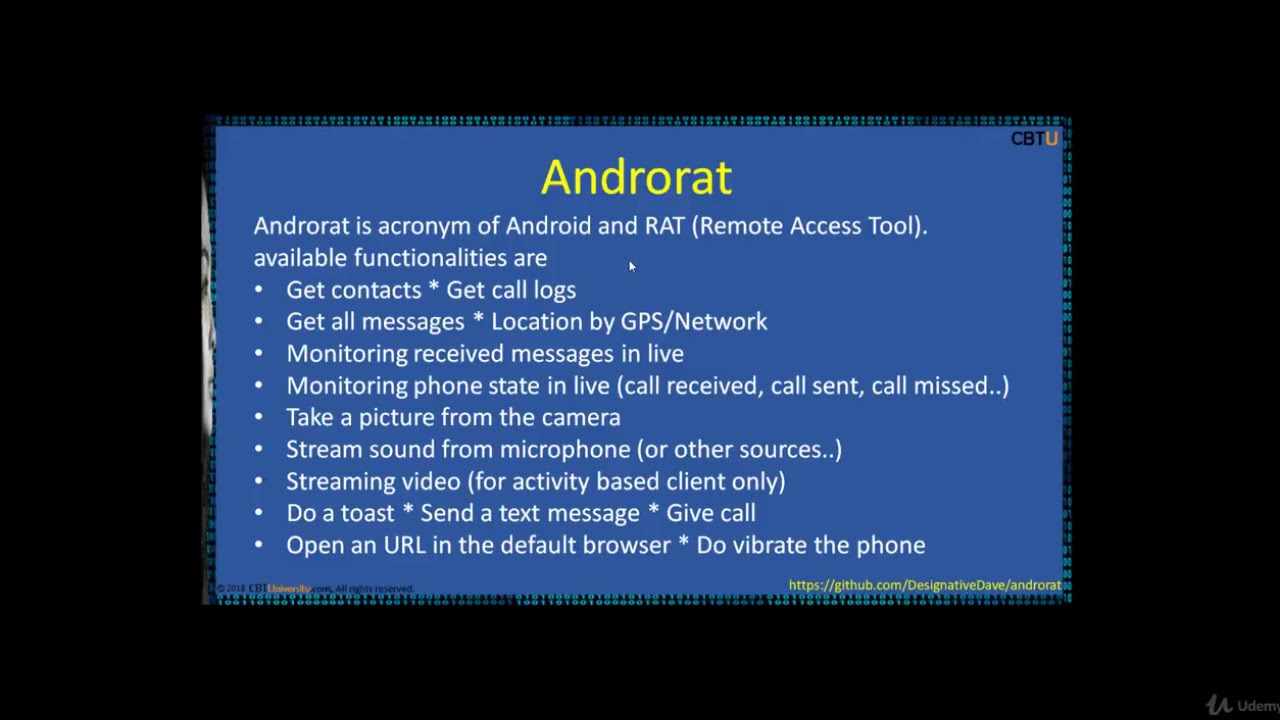
CEH16-2 Mobile Hacking tools
#Shells#TesteraircrackbasicsBeginnersburp suiteCompletecourseCybersecurityenumerationethicalethical hackerexpertfootprintingfreehackingHacking CourseHacking For Beginnershacking tutorialinformation securityInfosecitlearn hacking in banglamacchangermetasploitnmaponlinepass the hashpenetrationpenetration testerPentesterport scanningproxychainsreport writingreverse shellSecuritySQLtestingtrainingUdemyZero to Hero
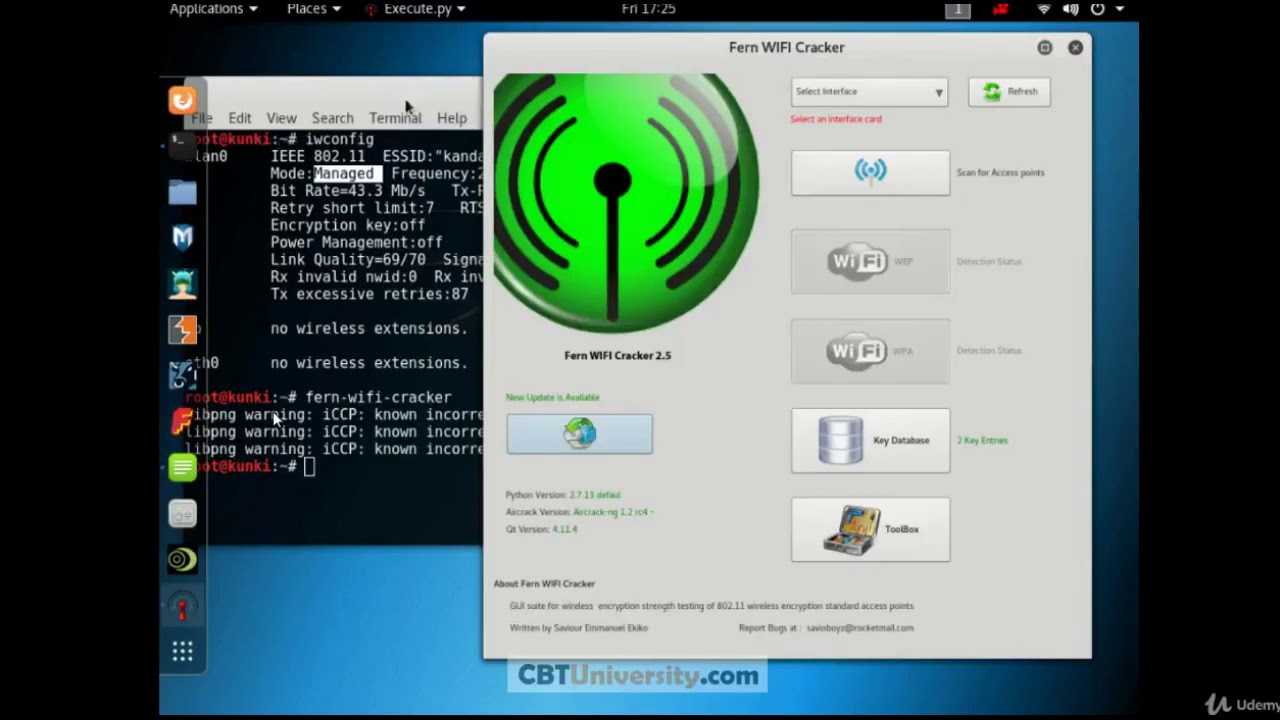
CEH 15 FERN wifi cracker
#Shells#TesteraircrackbasicsBeginnersburp suiteCompletecourseCybersecurityenumerationethicalethical hackerexpertfootprintingfreehackingHacking CourseHacking For Beginnershacking tutorialinformation securityInfosecitlearn hacking in banglamacchangermetasploitnmaponlinepass the hashpenetrationpenetration testerPentesterport scanningproxychainsreport writingreverse shellSecuritySQLtestingtrainingUdemyZero to Hero
Amazon Web Services AWS Zero to Hero
.NETAlgorithmsAmazonanalyticsandroidapacheapiASP.NETAssemblerAWSC#ciscocmsCSSDatabasedesignFreeDownloadBookGameshackinghardwarehtmlhtml5iOSJavajavascriptKindleLinuxMathematicsmicrosoftnetworknode.jsooporeillyPacktphpprogrammingpythonPythonMLAIrubySecurityseoSwiftWeb ServicesWindowsZero to Heroالربح من الانترنتاندرويدبايثونبرمجةتصميمتويترجافاجوجلسكربتسماعصامعمرفيس بوك
