Tag Archives: ethical

CEH18-3 Cloud Security Alliance
#Shells#TesteraircrackbasicsBeginnersburp suiteCompletecourseCybersecurityenumerationethicalethical hackerexpertfootprintingfreehackingHacking CourseHacking For Beginnershacking tutorialinformation securityInfosecitlearn hacking in banglamacchangermetasploitnmaponlinepass the hashpenetrationpenetration testerPentesterport scanningproxychainsreport writingreverse shellSecuritySQLtestingtrainingUdemyZero to Hero

Ethical Hacking with Python Hacking Tools
Cybersecuritycybersecurity expert pathethicalethical hackingethical hacking careerEthical Hacking Courseethical hacking course for beginnersethical hacking full courseethical hacking pythonethical hacking roadmapethical hacking tutorialethical hacking with pythonethical hacking with python hacking toolshackingkali linuxlearn ethical hackinglearn ethical hacking with pythonpythonpython hackingpython hacking toolspython tutorialWireshark

Learn Ethical Hacking using Python
codequscyber securityethicalethical hackingEthical Hacking Courseethical hacking for beginnersethical hacking full courseethical hacking pythonethical hacking tutorialethical hacking tutorial for beginnersethical hacking using pythonethical hacking with pythonhackerhackinglearn ethical hacking with pythonLearn PythonMoriohpython ethical hackingpython for beginnerspython for ethical hackingpython tutorialpython tutorial for beginnersSecurity
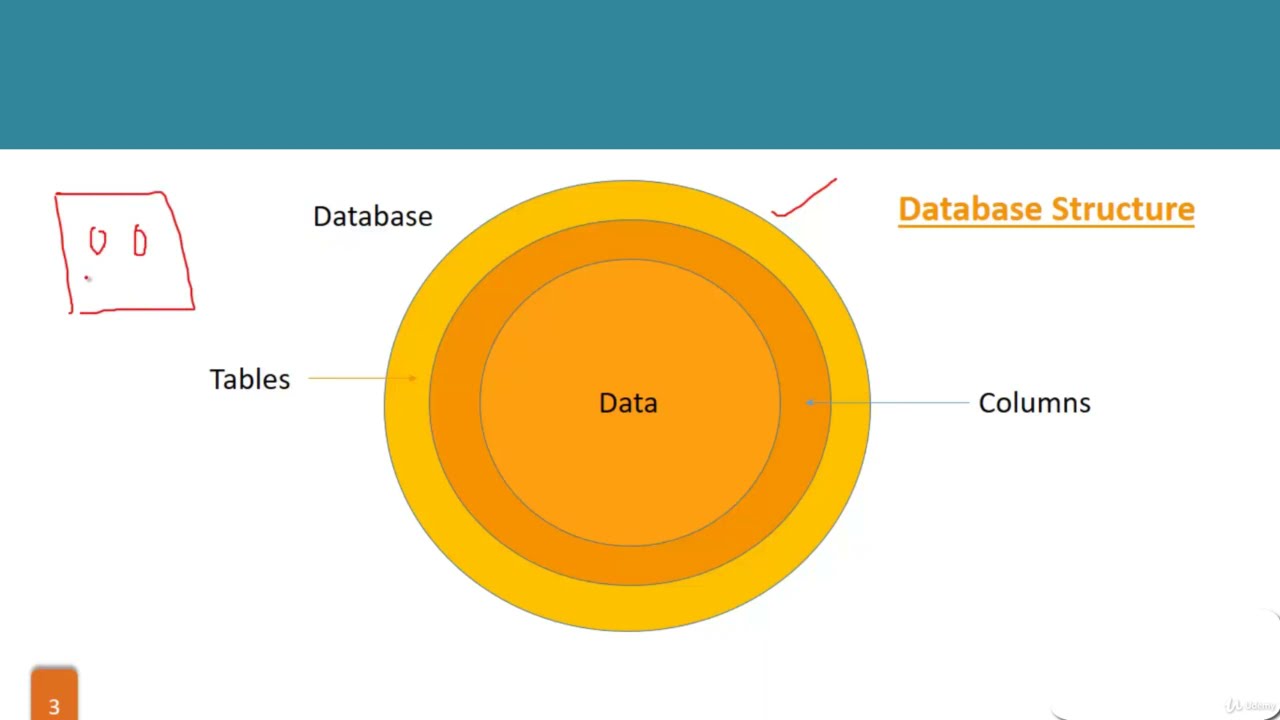
Cybersecurity Tutorial for Beginners: Network Operations
codequscyber securityCyber Security CourseCyber Security TutorialCybersecuritycybersecurity for beginnersCyberSecurity Tutorialcybersecurity tutorial for beginnersethicalethical hackinghackhackinginformation technologykali linuxMoriohnetworknetwork attacksnetwork fundamentalsnetwork operationsnetwork operations centernetwork operations center (noc)Network Securitynetworkingnetworking coursenmappenetration testingSecurityWeb Hacking
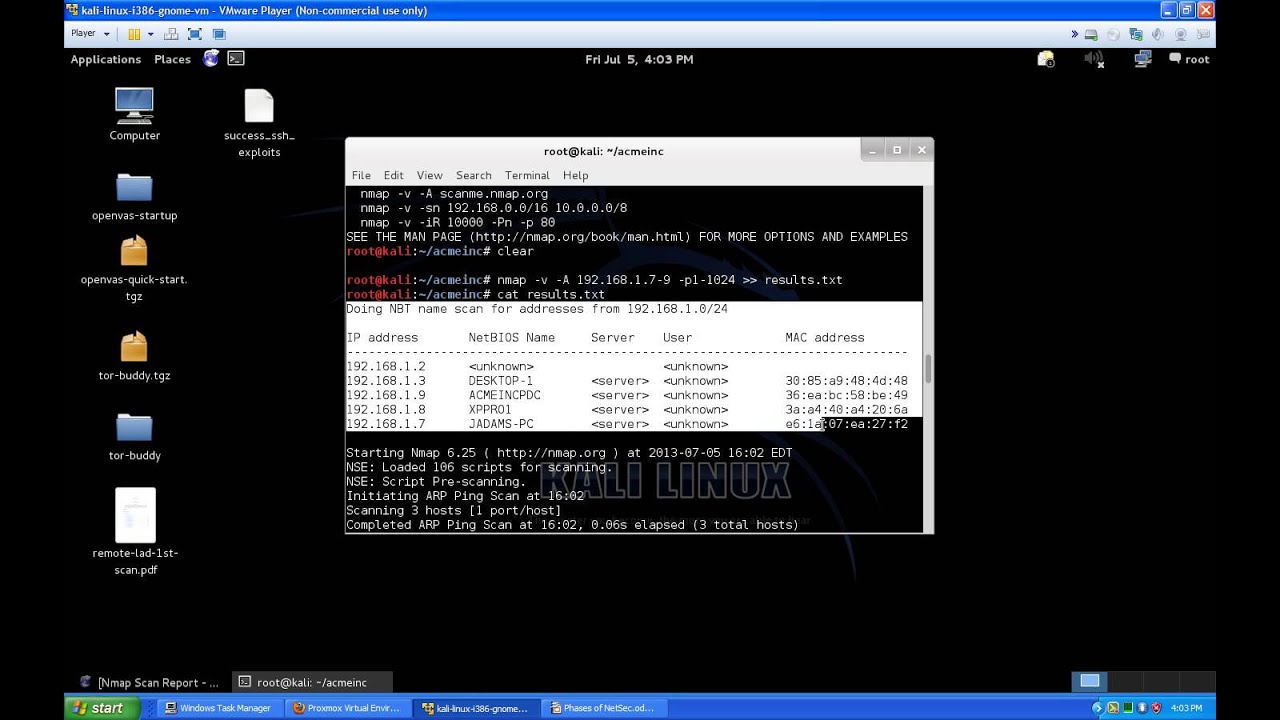
Network Security Phases Introduction For Beginners PT.3 Recon.
ArmitageComputerConfigurationdebianethicalexploithackerHacker (Character Power)hackingHow tohowtointroductionkali linuxLabLinuxmetasploitMicrosoft Windows (Operating System)networkNetwork Security (Organization Sector)nmappenetration testerpentestProxmoxProxmox VEProxmox Virtual EnvironmentSecurityServerTipstutorialvirtualvulnerabilityWindowszenmap
