Tag Archives: enumeration

CEH18-3 Cloud Security Alliance
#Shells#TesteraircrackbasicsBeginnersburp suiteCompletecourseCybersecurityenumerationethicalethical hackerexpertfootprintingfreehackingHacking CourseHacking For Beginnershacking tutorialinformation securityInfosecitlearn hacking in banglamacchangermetasploitnmaponlinepass the hashpenetrationpenetration testerPentesterport scanningproxychainsreport writingreverse shellSecuritySQLtestingtrainingUdemyZero to Hero
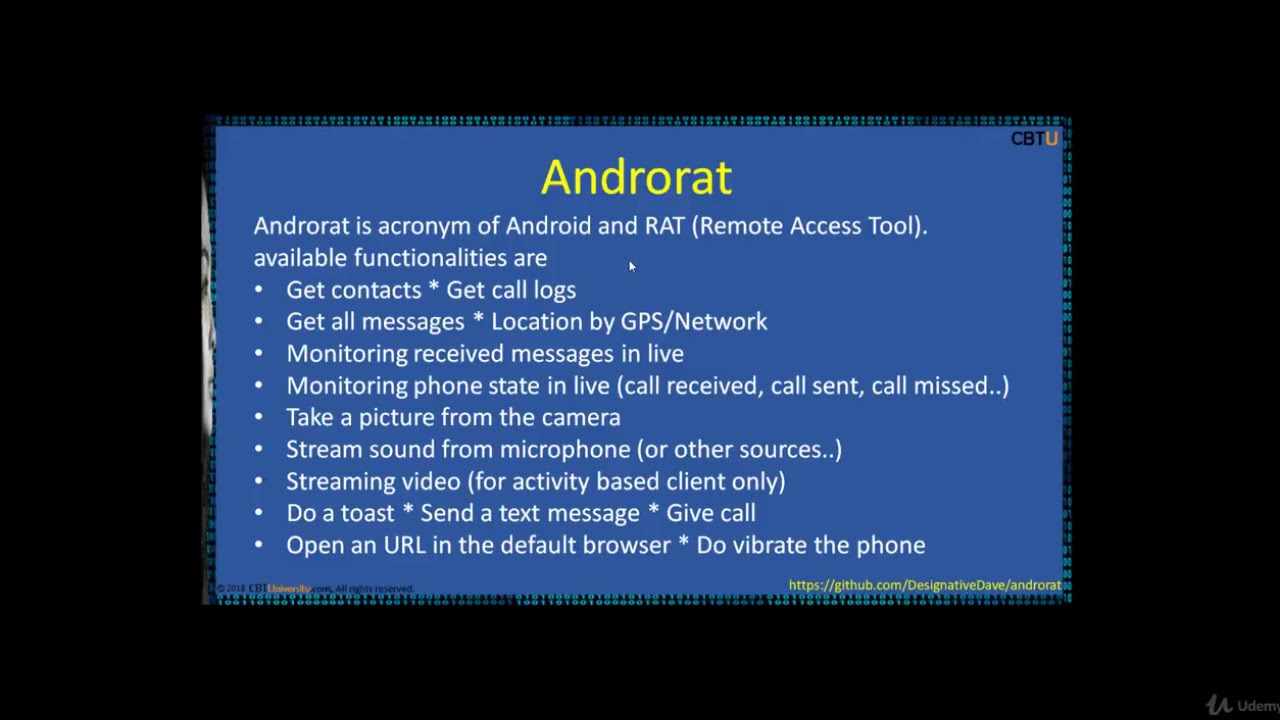
CEH16-2 Mobile Hacking tools
#Shells#TesteraircrackbasicsBeginnersburp suiteCompletecourseCybersecurityenumerationethicalethical hackerexpertfootprintingfreehackingHacking CourseHacking For Beginnershacking tutorialinformation securityInfosecitlearn hacking in banglamacchangermetasploitnmaponlinepass the hashpenetrationpenetration testerPentesterport scanningproxychainsreport writingreverse shellSecuritySQLtestingtrainingUdemyZero to Hero
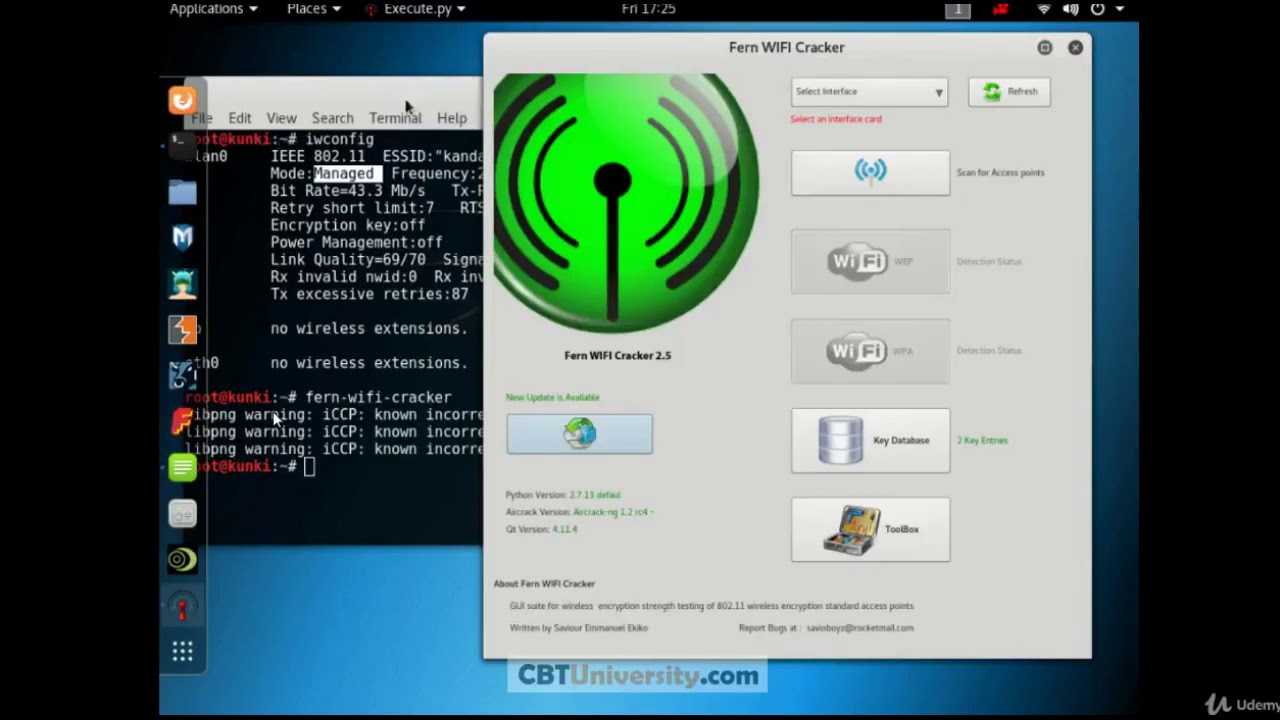
CEH 15 FERN wifi cracker
#Shells#TesteraircrackbasicsBeginnersburp suiteCompletecourseCybersecurityenumerationethicalethical hackerexpertfootprintingfreehackingHacking CourseHacking For Beginnershacking tutorialinformation securityInfosecitlearn hacking in banglamacchangermetasploitnmaponlinepass the hashpenetrationpenetration testerPentesterport scanningproxychainsreport writingreverse shellSecuritySQLtestingtrainingUdemyZero to Hero

Hackers type Learn Ethical Hacking With Kali Linux | Ethical Hacking Tutorial | Kali Linux Tutorial
#Burpsuite#Cpasswords#Ethicalhacker#Ethicalhackingtutorials#Gpp#Hackingcourse#Hackingforbeginners#Hackingtutorial#Hackthebox#Informationsecurity#Kerberoasting#Llmnrpoisoning#M4v3r1ck#Mobilephonehacking#Nikto#Notekeeping#Ntlmrelay#Passthehash#Penetrationtester#Portscanning#Psexec#Reportwriting#Reverseshell#Shells#Smbrelay#Tester#Tokenimpersonation#ZerotoheroenumerationhackingInfosecmetasploitnmaposcppentestPentesterpivotingpythontesting
Recent Posts
- Unix & Linux: Get common name (CN) from SSL certificate? (3 Solutions!!)
- DevOps & SysAdmins: How to update Group policy for the whole domain? (3 Solutions!!)
- DevOps & SysAdmins: GPO or Login script
- DevOps & SysAdmins: How to do exceptions in Group Policy?
- DevOps & SysAdmins: Microsoft Azure AD Connect Health Agent for sync 3.0.164.0 high CPU usage
