Tag Archives: cracking
Lab Overview & Needed Software | Ethical Hacking Course
Bug Bountycareer in cyber securitycareer in hackingcrackingctf lab for hackingcyber securitycyber yodhaethical hackingfree ethical hacking coursehackinghacking labhcaker vs crackerhohw to learn ethical hacking coursehow to get job in cyber securityhow to hunt bughow to practice hackinglearn ethical hacking freepassword attacksphases of hackingscope of ethical hackingscope of hackingtypes of hacker
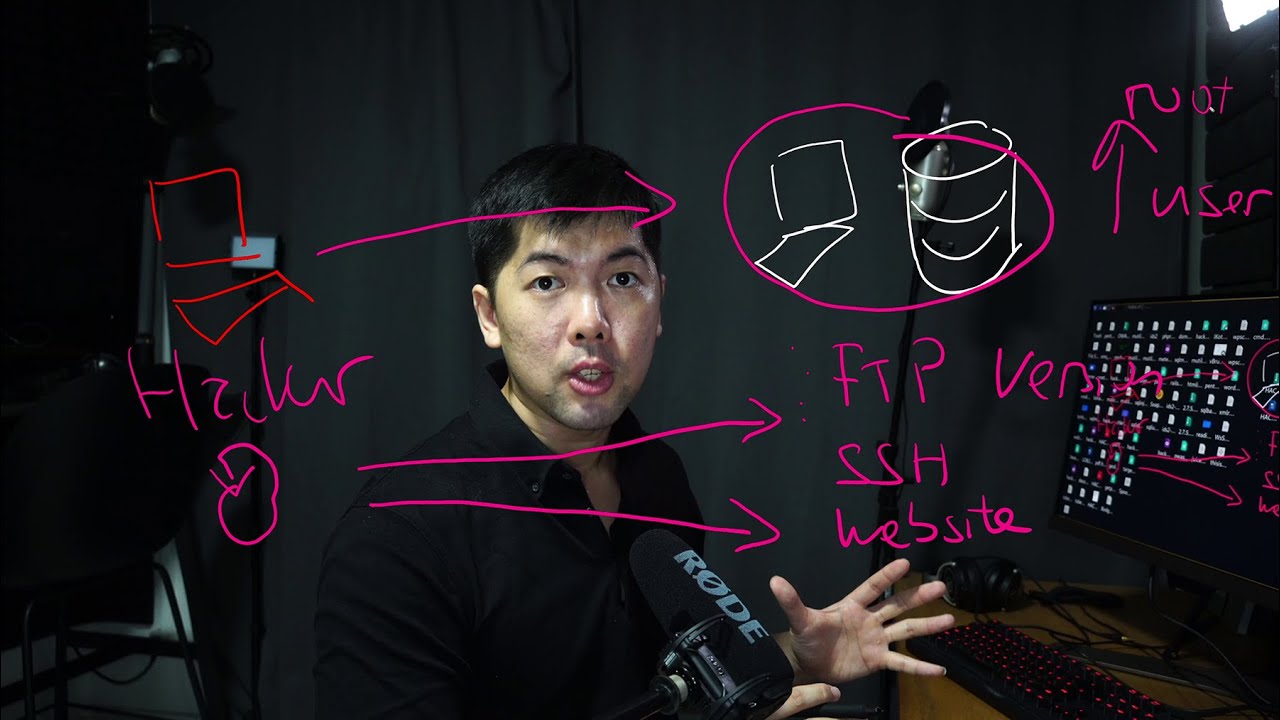


Nmap Tutorial for Beginners | Best tool
crackingcyber yodhaethical hackinghackinghacking toolhow to scan network using nmap toolnmao guidenmapnmap all commandsnmap bash shell scriptnmap basicsnmap bypass firewallnmap complete guidenmap complete tutorialnmap demonmap ethical hackingnmap examplesnmap firewall bypassnmap full tutorialnmap toolnmap tutorialscanning tool for hackersscanning tutorial
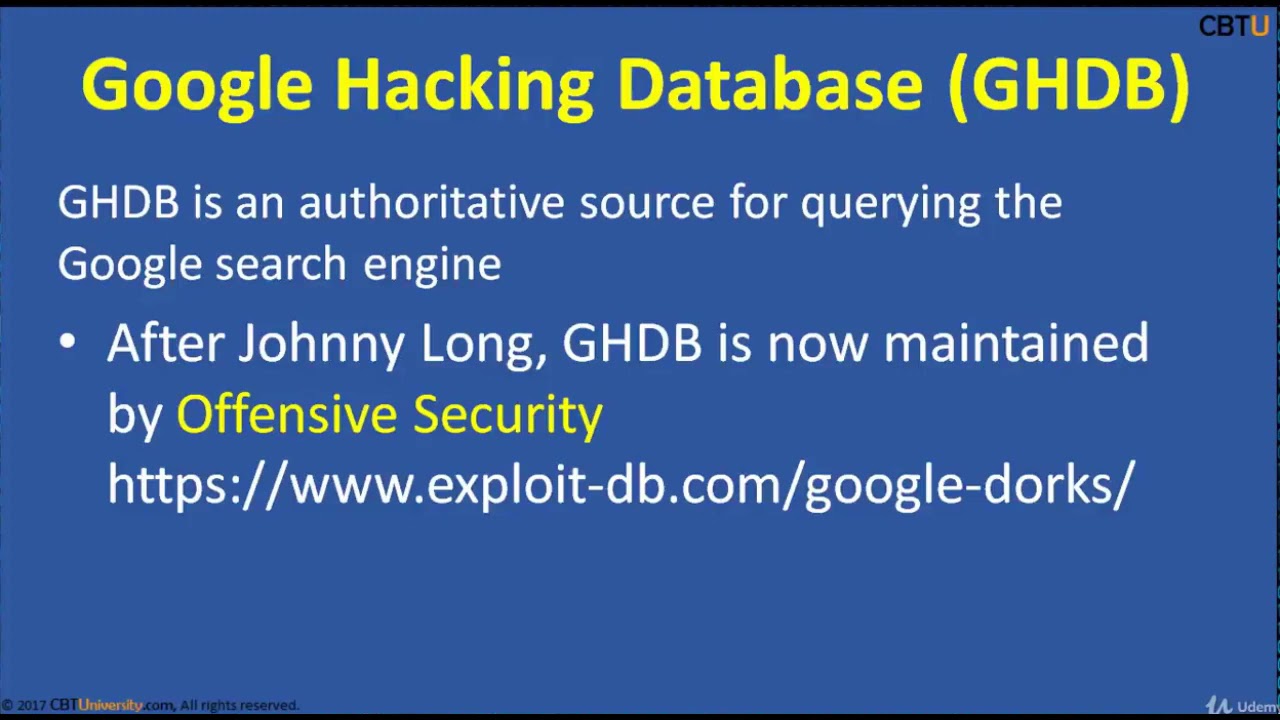
CEH2-3 Google Hacking Dorking
2015additionsaircrackbasicsBeginnersblackclicommandCompletecoursecrackcrackingenvironmentethicalexpertfootprintingforfreegreyguesthackhackerHacker (Interest)hackershackingHackshathdinstallinterfaceitKalikeylearn hacking in banglalineLinuxliveloggersmacchangernetworknmaponlinepenetrationprivateproxychainsreaverSecurityskillsSQLtermstestingtrainingUdemyvirtualvirtualboxVirtualBox (Software)vpnvpswhitewifiWindowswpawpa2
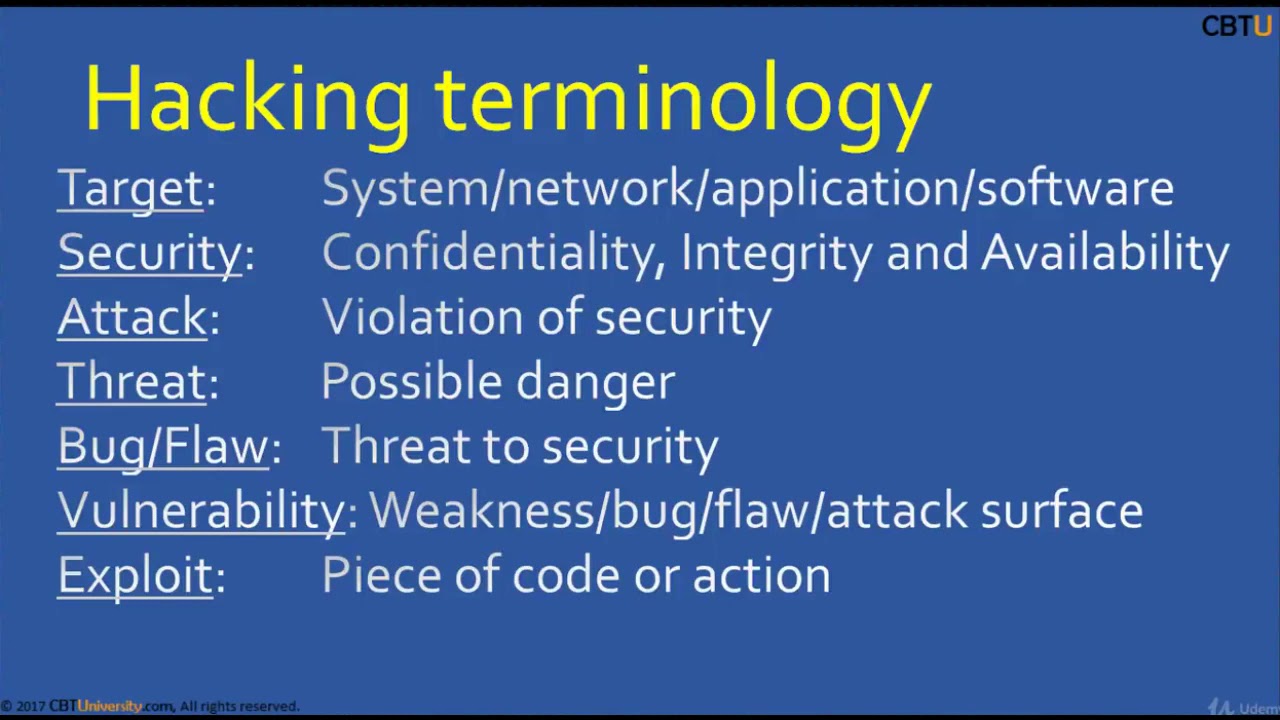
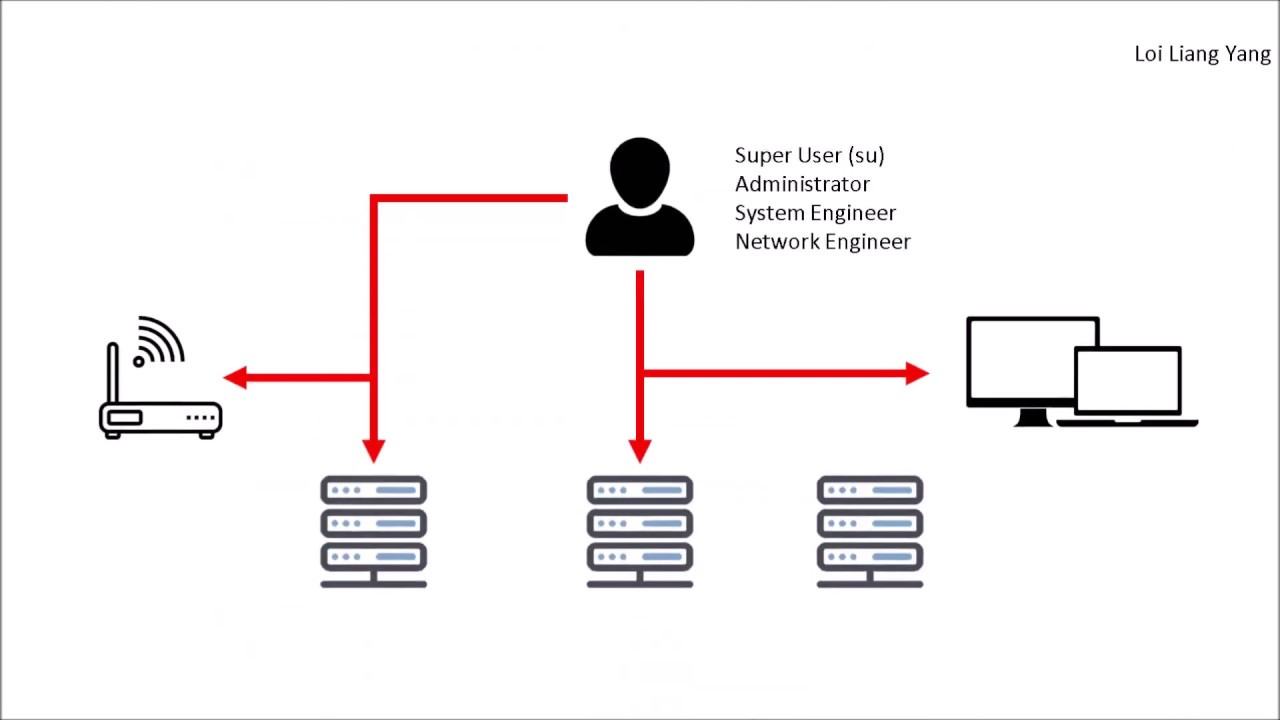
CEH1-1 Introduction to hacking
2015additionsaircrackbasicsBeginnersblackclicommandCompletecoursecrackcrackingenvironmentethicalexpertfootprintingforfreegreyguesthackhackerHacker (Interest)hackershackingHackshathdinstallinterfaceitKalikeylearn hacking in banglalineLinuxliveloggersmacchangernetworknmaponlinepenetrationprivateproxychainsreaverSecurityskillsSQLtermstestingtrainingUdemyvirtualvirtualboxVirtualBox (Software)vpnvpswhitewifiWindowswpawpa2

Recent Posts
- IAM4NFDI quickly explained
- Steganography (1/2) BsidesCT CTF 2018
- Pentagon calls Turkish drone shot down in Syria by US forces a ‘regrettable incident’
- Sodinokibi Ransomware Encrypts Hundreds of Dental Practices via IT Provider PerCSoft.
- #19 Method in Java | what is method overloading in java | Tutorials for beginners
